Anzenna
Modern businesses face threats from all angles – and some of the most dangerous risks come from within. Misconfigured devices, shadow applications, and users operating outside security policy can fly under the radar – until it’s too late.
That’s why Anzenna and Jamf teamed up. Anzenna is now a Jamf Solution partner and is listed on the Jamf Marketplace.
Our powerful integration combines Jamf’s industry-leading device management with Anzenna’s AI-powered risk visibility and remediation platform. The result? A clearer, smarter view of what’s happening across your organization – and the means to take instant action.
Total Risk Visibility. One-Click Remediation.
Imagine discovering that an employee quietly installed a fake AI tool that’s harvesting company data. Or realizing your organization is unknowingly paying for eight different versions of VPN software because no one has visibility into what’s actually being used. Maybe you’ve even been blindsided by an overuse notice from a vendor—only to find out you’ve been exceeding license limits for months. These are the kinds of risks that slip through traditional IT and security tools. That’s where Anzenna comes in.

(Caption: In July of 2024, a Disney employee upended his life when he downloaded an AI tool from GitHub to explore its capabilities. Unfortunately, he had accidentally downloaded a Trojan horse program allowing the attacker to access his personal device over several months. The attacker stole his personal info, including his 1Password account credentials, and the breach eventually extended into Disney’s inner systems leading to the theft and public exposure of over a terabyte of company data, including financial and strategy information.)
Anzenna is a fully agentless Insider Risk Management platform built for modern IT and security teams—redefining how organizations identify and respond to risk. At the core of this new paradigm is Agentic AI, which goes beyond automation to actively reason through gaps in your device and application data. When integrated with Jamf, Anzenna becomes a single source of truth for your environment, intelligently enriching inventory data by mapping users to devices, identifying shadow apps, and uncovering contextual insights. Agentic AI evaluates each application’s provenance, usage, and developer history—flagging past breaches, suspicious behaviors, or misaligned usage patterns. With every app scored and categorized by real risk factors, teams can move from insight to action instantly, remediating threats through the Jamf agent in just a few clicks.
Key Features & Capabilities
- Application Inventory Enrichment
Pull in accurate device and application data from Jamf, then enrich it using AI for deeper context. - Risk Scoring & Categorization
Understand who built an app, if they’ve been breached, and how risky it is – before it’s too late. - One-Click Remediation
Use Jamf’s native agent to disable apps, update policies, or quarantine devices – no new agents required.
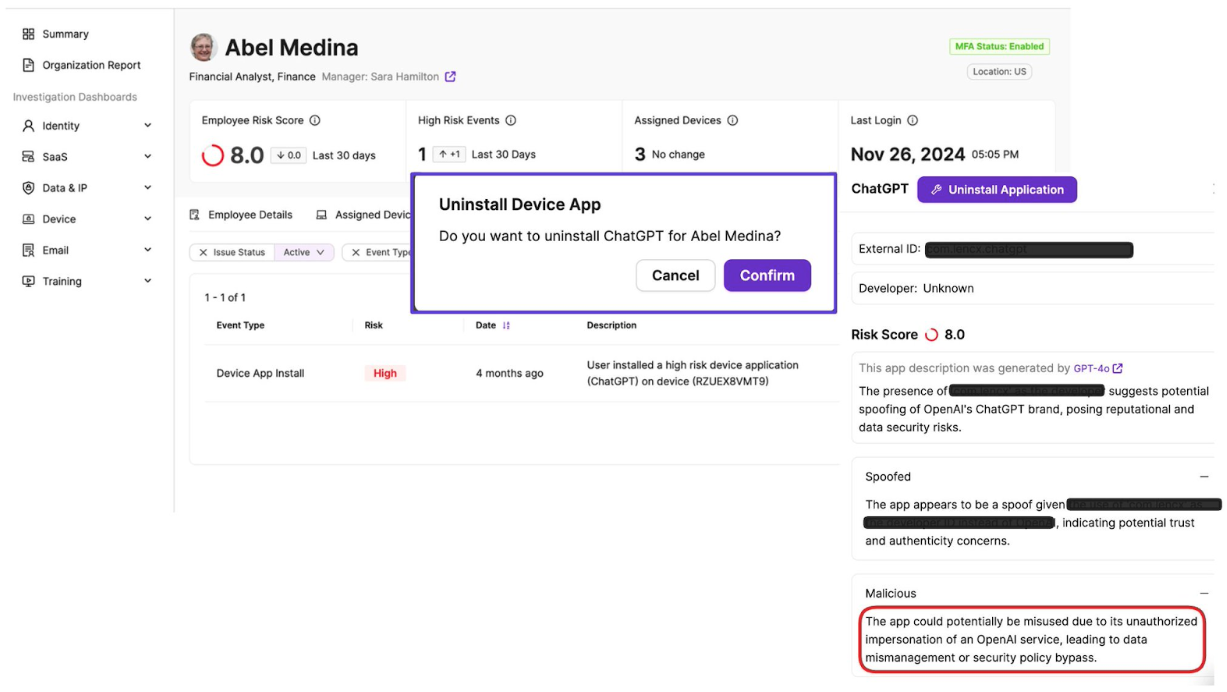
(Caption: Anzenna finds and uninstalls a fake version of ChatGPT)
- Roll-Up Risk Visibility
View risk across teams, departments, or your entire organization with consolidated risk scoring.
How It Works
- Secure API Connection
Establishing a secure connection between Anzenna and Jamf Pro is simple and fast. With just a few clicks, you can configure client credentials and enable seamless API integration. This ensures encrypted communication and authentication between systems without needing custom scripts or manual workarounds. Once connected, data flows securely, enabling real-time insights and automation. The setup is designed to be both enterprise-ready and frictionless for IT teams. - Data Enrichment
Anzenna’s Agentic AI engine enhances your visibility by filling in the critical gaps left by standard datasets. It intelligently maps users to devices, providing accurate associations that are essential for meaningful risk assessments. The AI also verifies application developers, helping to flag unknown or suspicious sources. Each device, app, and user is assigned a contextual risk score, making prioritization easier and more precise. This enriched context empowers teams to act on insights with confidence, not guesswork. - Remediation & Enforcement
With Anzenna and Jamf working together, you can move from detection to action instantly. The Jamf agent allows you to disable risky applications, push policy updates, or even quarantine compromised devices—all in just a few clicks. There’s no need for extra infrastructure, scripting, or manual triage. This rapid response capability dramatically reduces time-to-containment and helps maintain a secure device fleet. It’s enforcement made simple, scalable, and effective. - Consolidated Reporting
Anzenna pulls together data from Jamf and other sources to give you a complete view of device and application posture. All insights are displayed in a single, unified dashboard, making it easy to spot trends and identify issues across your environment. Reports are enriched with context and actionable flags, not just raw data. This clarity enables faster decision-making and improves team alignment around remediation priorities. With consolidated reporting, you’re no longer chasing down fragmented insights—you’re acting on a full picture.
Security & Compliance
- SOC2 Type II Certified: Your data and processes meet rigorous standards.
- Microsoft 365 Pentested: Verified security posture in real-world scenarios.
- Minimal footprint on your environment: no new agents required to setup.
The Result?
Reduced Complexity: Eliminate guesswork by automatically categorizing thousands of applications.
Accelerated Time-to-Value: See tangible security improvements within days of connecting Jamf to Anzenna.
A Partnership Built to Scale
Anzenna is proud to be a Jamf Solution Partner. Our collaboration is grounded in a shared vision: to give teams the tools they need to see clearly and act quickly. We offer co-branded support guides, joint enablement resources, and a detailed onboarding process that helps customers connect Jamf to Anzenna in minutes—not days.
Seeing Is the First Step to Believing
Connect with Anzenna, discover what’s been hiding in plain sight and start your free 30-day trial.
As a former CISO with over 25 years of experience, I’ve witnessed some of the most damaging security breaches—most of which were caused by Insiders. Insiders refers to employees, contractors, and anyone with legitimate access to an organization’s environment. Whether intentional or accidental, insider actions remain a primary vector for cyber threats.
Common Insider Risks
- Insiders often use weak or reused passwords.
- Insiders install rogue applications and browser extensions on company devices.
- Insiders make sensitive data public for convenience.
- Insiders fall victim to repeated phishing attacks.
- Insiders bypass security protocols using Shadow IT.
- Insiders often obtain or retain more access than necessary for their roles.
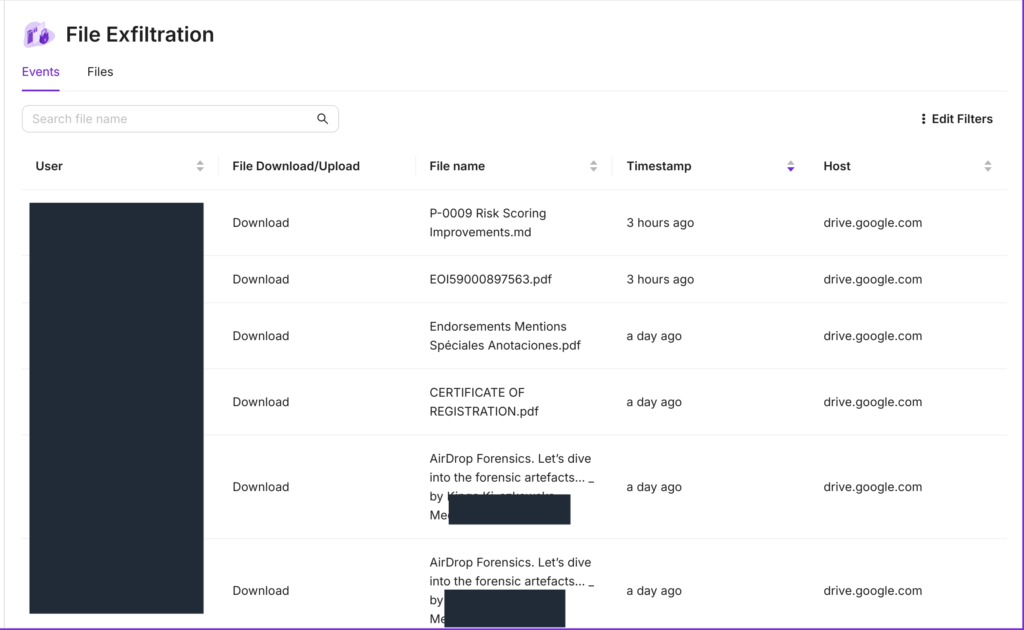
- Insiders exfiltrate company and customer sensitive data.
- Insiders exfiltrate company code to personal repositories.
- Insiders are socially engineered into leaking company data.
- Insiders leave secrets exposed in code.
- Insiders get corporate machines infected with ransomware.
- Departed insiders retain unauthorized access.
- Insiders bridge home networks to corporate and customer environments.
These examples highlight that
insider risk extends across the entire security program and is not limited to DLP or data controls.
Attackers actively target insiders because they are an effective and often overlooked entry point. These breaches not only compromise sensitive data but also disrupt business operations and weaken organizational resilience.

The Security Gap: Why Current Approaches Fall Short
Despite growing threats, security investments have largely focused on technology and compliance—leaving insider risks inadequately addressed.
Consider this:
If a thief steals your car keys, the car cannot distinguish between you and the thief.
Similarly, a security strategy centered on devices, events, networks, accounts and compliance lacks the context to identify true insider risks.
To secure an organization effectively, security must be people-centric.
The Security Dilemma: Trust vs. Protection
Organizations rely on insiders to act responsibly, but mistakes are inevitable. Security teams face the challenge of
enabling productivity while enforcing strong protections.
So, how can security leaders tackle this growing threat without stifling business operations?
Three Critical Steps to Strengthen Insider Risk Management
1. Enforce Strong MFA (Preferably Passkeys) Immediately
Multi-Factor Authentication (MFA) is one of the most effective controls to prevent unauthorized access.
If you haven’t already implemented phishing-resistant MFA across insiders, vendors and customers, now is the time.
2. Shift to an Employee-Centric Security Posture
Most security tools offer only machine or event-level insights—not a
holistic, user-centric view of risk.
Even when employee-level data exists (e.g., phishing reports), it is often fragmented and fails to provide a complete picture.
Security leaders may assume their existing tools offer sufficient protection, but
without a single, people-centric source of truth, it’s impossible to validate whether security controls are truly effective.
Think of insider risk like a pandemic—you need accurate insights into:
- Who is at risk?
- How many repeat offenders exist?
- What security variants (types of insider threats) are emerging?
- Who is resilient, and who needs additional safeguards?
Time is the most valuable asset for security teams. Reducing noise and
identifying high-risk insiders with precision
is critical to an effective defense strategy.
3. Build Transparency and Training into Your Insider Risk Strategy
Insiders should be aware that
insider risk is being monitored
—not as a punitive measure, but as a way to enhance security and learning.
Mistakes should be
treated as opportunities for improvement
and should drive
targeted user-level controls
rather than broad, restrictive policies.
A
data-driven
approach to insider risk ensures alignment with business objectives.
When security policies are backed by real-world data, they gain credibility and minimize resistance from both leadership and employees.
Final Thoughts
Insider risk is not just an IT issue—it’s a
business-critical challenge.
Addressing it requires a proactive, data-driven, and employee-centric approach.
Security teams must rethink traditional models and adopt strategies that both protect the organization
and empower insiders to work securely.
The question is no longer if insider risk will impact your business—but when.
Are you ready?
Anzenna’s agentic AI security platform takes cybersecurity beyond detection—automating real-time threat remediation to stop insider risks, IP exfiltration, rogue apps and compliance violations instantly. By seamlessly integrating with existing security tools, Anzenna eliminates manual effort, enforces security policies at scale, and ensures organizations stay protected without added complexity.
[San Francisco, CA] – Anzenna, the pioneer of Human-Centered Security, today announced its Winter Product Release, introducing the first agentic AI security platform that delivers pinpoint-accurate risk identification and real-time, automated remediation across an organization’s existing security ecosystem. Unlike traditional security tools that focus on perimeter or endpoint protection, Anzenna zeroes in on the most critical and overlooked security element: human behavior.
By seamlessly integrating with existing security tools such as SIEMs, EDR, DLP, IAM, Cloud and enterprise security orchestration tools as well over 50 common enterprise applications such as Google Workspace, Microsoft 365, GitHub, Anzenna automates detection and enforcement at scale, requiring no agents or complex setup. Security teams can now stop insider risk, prevent IP exfiltration, and remediate compliance violations within minutes without hiring additional analysts or overloading existing tools.
“We are redefining what’s possible in security operations by introducing agentic AI technology that doesn’t just surface risks but takes action instantly,” said Ganesh Krishnan, Founder and CEO of Anzenna.
“Many security teams are already managing dozens of tools, making it critical that any new technology enhances rather than complicates existing workflows. Anzenna is designed to fit seamlessly into any security stack—serving as a user-centric control plane that aggregates, prioritizes, and automates risk mitigation without adding operational burden.”
Security and Compliance Actions, Automated in Minutes
Anzenna’s AI-driven platform enables security teams to:





AI-Powered Remediation Across the Entire Security Ecosystem
Traditional security solutions detect threats but require extensive manual effort to investigate and remediate. Anzenna’s agentic AI-driven automation eliminates this friction by integrating directly with security teams’ existing tools to remediate policy violations in real-time.
Key features of the Winter Release include:
- Agentless, Instant Deployment – Anzenna’s cloud-native platform requires no agents, no
complex setup, and no disruption to existing security workflows. Organizations gain instant visibility into user actions, SaaS applications, and identity security risks. - Seamless Integrations for Automated Action – Out-of-the-box integrations with over 50 enterprise applications, identity providers, and security orchestration platforms ensure organizations can enforce security policies across their existing toolsets.
- Pinpoint-Accurate Risk Identification – AI-driven insights distinguish real threats from noise, enabling security teams to act on the most critical risks without alert fatigue.
- Automated Remediation at Scale – Security teams can automatically revoke access, remove risky applications, block unauthorized data sharing, and enforce compliance policies with minimal effort.
A New Era of Human-Centered Security
With hybrid work environments, SaaS sprawl, and identity-based attacks on the rise, security teams face growing pressure to reduce risks without adding friction to the business. Anzenna’s agentic AI platform ensures companies can proactively protect users, applications, and identities, without slowing down productivity.
“With our Winter Release, we are proving that security can be both proactive and effortless,” added Ganesh Krishnan. “By focusing on people, behaviors, and automation, Anzenna is closing the gaps that traditional security tools leave open, allowing teams to focus on innovation rather than chasing security incidents.”
Anzenna is offering enterprises to apply for a free proof-of-concept pilot for the month of February and March. Please visit www.anzenna.ai
Anzenna is pioneering Human-Centered Security with the first Agentic AI-driven platform that identifies security and compliance risks with pinpoint accuracy and automatically enforces remediation actions across existing security tools. By focusing on the human element, where most security incidents originate, Anzenna enables companies to proactively prevent threats, enforce security policies in real- time, and maintain compliance without disrupting productivity.
“Have I Been Pwned” (HIBP) is an online service that allows users to check if their personal data has been compromised in a data breach. Created by Troy Hunt, HIBP collects and analyzes data from breaches, helping people secure their digital presence.
Every other day, another company makes headlines as the victim of a data breach. While these breaches are a constant threat to enterprises worldwide, it’s impractical to prevent employees from using everyday SaaS tools in their jobs. Protecting sensitive information is paramount for enterprises, and the first step is knowing if and to what extent your data has been compromised. This is where HIBP comes into play. By integrating with HIBP, enterprises can automatically monitor their users for breaches and trigger automatic remediation via products like Anzenna, significantly enhancing their security posture.
Where does Anzenna come in?
Anzenna helps enterprises detect, deter, and disrupt insider risk by combining intelligence from a myriad of security tools, including Identity management, MDMs, Endpoint solutions, External sources and more.
HIBP seamlessly fits into this model, enhancing existing signals and assisting incident response teams in putting the pieces together. For example, reused credentials leaked in an identity breach can lead to a risky login that might not be blocked by the identity provider. This could allow an attacker to exfiltrate data or hold the company hostage.
Early and proactive remediation can prevent such situations. When an enterprise admin sees an employee’s external breach on the Anzenna dashboard, they can immediately reach out to the employee via Slack or Teams and ask them to change their password. Alternatively, they can use our identity provider integrations to force a password reset on the employee’s behalf.
Benefits for Enterprises
1. Proactive Threat Detection
Integrating Anzenna and HIBP into your enterprise security infrastructure enables proactive monitoring of user accounts and insider risk. By regularly checking email addresses and usernames against the HIBP database, you can identify compromised accounts early and take immediate action to mitigate risks. This early detection is crucial in preventing further exploitation of breached data.
2. Enhanced User Security
When a breach is detected, you can promptly notify affected users, advising them to change their passwords and take other necessary security measures. For corporate accounts, enterprises can also force a password reset for the employee.
3. Strengthened Compliance
Many industries are governed by strict data protection regulations, such as GDPR, HIPAA, and CCPA. This integration can help companies meet these regulatory requirements by demonstrating a proactive approach to data security and breach notification. This not only avoids hefty fines but also maintains the enterprise’s reputation.
Conclusion
Incorporating Anzenna and “Have I Been Pwned” into your enterprise’s security framework is a strategic move towards bolstering data protection. This integration enables proactive breach detection, enhances user security, automates monitoring, strengthens compliance, and supports comprehensive risk assessments, making it a valuable combination in the fight against cyber threats.
Contact us to take a proactive stance in securing your enterprise against the ever-evolving cyber threat landscape.
In today’s world of cloud-first modern enterprises, the web browser is the entrypoint to many critical company resources. Sensitive corporate credentials, session tokens, MFA authenticated services, emails and documents – ranging from employee pay stubs to client contracts – live in resources such as cloud drives and third party SaaS applications. In addition to corporate resources, it is also common for employees to access personal websites on company machines. Hence monitoring and protecting browser usage within a corporate setting is paramount.
Companies can go about this by installing agents on the user OS but there are several problems with this approach including: Significant time and resources needed to deploy and configure; resiliency issues as demonstrated with recent outages; missed context on user behavior which increasingly takes place on the browser; performance impact on employee machines; poor employee privacy control.
While agents may be appropriate in some situations, the majority of customers demand lightweight and resilient approaches that allow security teams to get the right visibility while preserving corporate resiliency, employee privacy & company culture.
In order to enhance its agentless insider-risk and human security offering, Anzenna has released an optional browser extension that customers can deploy to solve specific browser level security problems while protecting employee privacy.
Our browser extension securely tracks employees’ security posture on the web. The scope of data collection is centrally managed by the security team within a specific customer environment. Errors are sandboxed to the browser and can be unilaterally rolled back because they don’t touch the underlying OS.
Here are some key use cases we address via the browser extension:
- Data exfiltration: Track downloads of sensitive company resources (e.g. documents originating from the corporate drive) and keep track of where they have been uploaded and shared. This is especially important with the increasing use of AI tools such as GPT to perform tasks on company resources. The scope of data collection is configurable by security admins to balance employee privacy with risk visibility.
- Shadow IT tracking : Employees may use unapproved applications (e.g., note taking, management, and AI tools) to perform day-to-day tasks. Since these applications may not be accessed via the enterprise SSO, security teams have no visibility over them. Any data breaches in these applications would go undetected and leak sensitive company information.
- Unsafe password usage : Track employee password hygiene. Are they using password managers or sharing passwords across websites? Have their credentials been compromised in a recent security breach?
All of the collected data is easily viewable and queryable via the Anzenna admin interface.
Anzenna serves as the ultimate source of truth for people-security data, enhancing existing controls and pinpointing areas needing reinforcement. Leveraging AI to forecast and curb insider risks, Anzenna proactively counters both malicious and accidental threats within minutes, offering a modern alternative to traditional siloed security measures such as UEBA, SaaS Security, and conventional security training.
Contact Anzenna to learn more and get a free Insider Risk Assessment today!
Over the past few weeks, we’ve embarked on an exciting project to enhance Anzenna’s insider security monitoring capabilities by integrating with Snowflake, a leading cloud-based data warehousing platform. With this new integration, our customers can now enjoy seamless monitoring of their Snowflake environments, with up to date information on data sharing and use. This means quicker identification of potential threats and more effective risk management. In this update, we delve into the technical details of this integration, highlighting our use of OAuth for authentication and Snowflake’s SQL HTTP endpoint to monitor and analyze database usage.
You might wonder what a Snowflake integration has to do with insider risk. While recent attention has focused on enabling MFA for Snowflake, the real security risk lies in how securely insiders use it, given the vast amount of sensitive information stored within. For more details, refer to our Insider Risk 101 blog post: https://www.anzenna.ai/holistic-insider-risk-management-the-time-is-now/.
Integration Overview
Our integration with Snowflake follows a structured yet dynamic framework, beginning with the customer signup process. When a new customer joins our platform, they undergo a streamlined signup process that generates and stores OAuth credentials. These credentials are essential for establishing a secure connection to their Snowflake instance, allowing our system to authenticate and interact with Snowflake seamlessly.
Setting Up a Security Integration in Snowflake
Setting up a security integration in Snowflake involves creating an OAuth-based connection. This process starts by configuring your Snowflake instance to recognize our application as a secure client.
This is done by first setting up a security integration within your Snowflake instance:
CREATE SECURITY INTEGRATION MY_SNOWSQL_CLIENT
TYPE = OAUTH
ENABLED = TRUE
OAUTH_CLIENT = CUSTOM
OAUTH_CLIENT_TYPE = 'CONFIDENTIAL'
OAUTH_REDIRECT_URI = 'https://example.com/callback'
OAUTH_ISSUE_REFRESH_TOKENS = TRUE
OAUTH_REFRESH_TOKEN_VALIDITY = 86400;
The OAUTH_REDIRECT_URI is a critical component, as it ensures that the authorization code grant is safely passed back to your application. For instance, during development, this URI might point to localhost:<yourport>, but in production, it should be set to a secure, publicly accessible URL.
Handling an OAuth Callback
Here’s an example of handling an OAuth callback in Go:
// add the handler function to the router for your golang server
mux.HandleFunc("/callback", callback)
func callback(w http.ResponseWriter, r *http.Request) {
// Capture the auth code grant from the URL
AuthGrant := r.URL.Query().Get("code")
oauthConfig := &oauth2.Config{
RedirectURL: "http://example.com/callback",
ClientID: os.Getenv("SNOWFLAKE_CLIENT_ID"),
ClientSecret: os.Getenv("SNOWFLAKE_CLIENT_SECRET"),
Endpoint: os.Getenv("SNOWFLAKE_TOKEN_ENDPOINT"),
}
token, err := oauthConfig.Exchange(r.Context(), AuthGrant)
if err != nil {
log.Println(err.Error())
http.Redirect(w, r, "/", http.StatusTemporaryRedirect)
return
}
// Persist or use token here
PersistToken(token)
w.WriteHeader(http.StatusOK)
}
To use the token later, it is retrieved from storage and used to construct an OAuth2-based HTTP client that can refresh the token as needed using:
client := oauth2.NewClient(ctx, TokenSource)
Monitoring and Data Analysis
Once authenticated, our system leverages the stored OAuth tokens to fetch data from several key Snowflake tables, including users, roles, shares, and usage_history. This data retrieval is facilitated through Snowflake’s SQL HTTP endpoint documented here: https://docs.snowflake.com/en/developer-guide/sql-api/intro, enabling us to execute SQL queries and obtain the necessary information efficiently.
Example Query: Data Sharing Monitoring
SELECT * FROM SNOWFLAKE.ACCOUNT_USAGE.QUERY_HISTORY WHERE REGEXP_LIKE(QUERY_TEXT, 'create\\s+share\\s.*','i') OR REGEXP_LIKE(QUERY_TEXT, '\\s+to\\s+share\\s.*','i') AND START_TIME >= DATEADD(HOUR, -24, CURRENT_TIMESTAMP());
Security Monitoring and Threat Detection
The gathered data is meticulously analyzed to monitor database usage and identify potential security risks. Our analysis focuses on detecting unusual patterns, unauthorized access, and other indicators of insider threats. Some of our current detections for our Snowflake integration include MFA account status, data exfiltration, and data sharing. By continuously monitoring and scrutinizing this data, we provide our customers with actionable insights to help safeguard their data assets.

This integrated approach ensures robust security monitoring and aligns with our mission at Anzenna to detect and prevent insider risks. By extending our monitoring capabilities to Snowflake, we continue to iterate on offering our customers a comprehensive solution to protect their sensitive information.
Contact Anzenna to learn more and get a free Insider Risk Assessment today!
Did you know that 68% of security breaches are caused by insiders?
Despite this alarming statistic, most security measures focus on perimeter defenses to keep external hackers at bay. While perimeter defenses are necessary, they are not sufficient. External hackers often seek to exploit insiders because they are often vulnerable. Therefore, it’s critical to develop a holistic understanding of insider risk posture and drive your security program accordingly.
Let’s clarify what insider risk truly means. Traditional views focus on malicious employees, the so-called “bad apples.” While these individuals pose a threat, they only account for about 1-5% of insider-related issues. The remaining 95-99% stem from well-intentioned insiders making accidental or negligent mistakes while performing their duties.
To effectively mitigate insider risk, it’s also essential to identify, understand, and manage these accidental and negligent mistakes that occur regularly within your organization. These are the mistakes that are most likely to lead to security breaches and put your company at risk.
Here are some examples:
Credential Stuffing: This attack method is on the rise and significantly contributes to breaches because humans often reuse credentials. This is a prime example of accidental or negligent insider risk. Do you monitor your employees to ensure they aren’t reusing corporate credentials on third-party sites?
Data Exposure: Employees frequently need to share information both internally and externally during their work. However, simple mistakes can lead to the inadvertent sharing of PII, PHI, and financial information, which could trigger disclosure requirements. This risk isn’t limited to collaboration tools but extends to big data environments like Snowflake. Do you have monitoring in place to address this?
Device Posture: Companies rely on their employees to keep corporate & BYOD devices and data secure. However, attackers target employees, attempting to get them to install rogue applications and browser extensions to take over their devices and sessions to critical applications, even if strong authentication methods like passkeys or MFA are enabled. Do you have comprehensive monitoring in place for applications installed, infection rates, and device posture gaps across all devices employees use to access your network?
The list goes on, including unsafe SaaS usage, Phishing susceptibility, malicious data exfiltration & misuse of admin privileges among others.
A holistic approach to insider risk involves understanding it across all these dimensions, attributing specific risks to individual insiders, and then implementing guardrails and deterrence measures backed by appropriate data and justification. The good news is that this no longer requires months of effort.
Contact Anzenna to learn more and get a free Insider Risk Assessment today!
We are happy to announce that Anzenna has achieved SOC 2 Type II compliance in accordance with American Institute of Certified Public Accountants (AICPA) standards for SOC for Service Organizations also known as SSAE 18. Achieving this standard with an unqualified opinion serves as third-party industry validation that Anzenna provides enterprise-level security for customer’s data secured in their system.
Anzenna Inc. was audited by Prescient Assurance , a leader in security and compliance attestation for B2B, SAAS companies worldwide. Prescient Assurance is a registered public accounting in the US and Canada and provides risk management and assurance services which includes but is not limited to SOC 2, PCI, ISO, NIST, GDPR, CCPA, HIPAA, and CSA STAR.
An unqualified opinion on a SOC 2 Type II audit report demonstrates to Anzenna’s current and future customers that they manage their data with the highest standard of security and compliance.
Before the SOC2 Type II, we also obtained our Microsoft 365 compliance which is an independent security assessment by Microsoft.
Many thanks to our customers for entrusting us with their data along with Microsoft and Prescient Assurance for helping us implement the highest security standards for them.
Microsoft has rolled out an exciting data security and privacy program within the software industry, especially with startups like Anzenna. This initiative is called the “Microsoft 365 App Compliance program”, and signifies a significant leap forward in guaranteeing the protection and confidentiality of sensitive data in your startup journey and building higher levels of trust from day 1.

Mission
The mission of this program is to offer confidence to your customers as a software vendor that data security, privacy and protection systems are in place. Achieving this trust isn’t just a one-step process; it’s an evolving journey that starts with demonstrating a strong commitment to data security and privacy.
By acquiring the Microsoft 365 App Compliance Certification, startups can demonstrate their dedication to safeguarding sensitive information, assuring customers that their data is in reliable hands.
Our Experience with Microsoft
At the core of Microsoft 365’s app compliance certification is a robust foundation anchored in industry-leading standards such as ISO 27001 and SOC 2. This program rigorously evaluates applications, ensuring unwavering adherence to stringent security and compliance protocols.
Our engagement with Microsoft in pursuing the Microsoft 365 App Compliance Certification was profound and transformative. We are dedicated to upholding high-security standards, and this independent certification process helped us strengthen those standards even further.
Microsoft’s certification analysts expect a comprehensive review of documentation as part of the initial submission. This includes detailed information on our app, supporting infrastructure, and supporting documentation. By proactively providing this documentation, we aimed to streamline the assessment process and demonstrate a commitment to transparency.
Microsoft has established certain automatic fail criteria that demand special attention. This process extended beyond mere checklist completion; it was an evidence-driven endeavour where each assertion was substantiated with concrete proof. It necessitates a comprehensive presentation of evidence.
These include elements such as API permissions following the principle of least privilege, the provision of a penetration testing report when required, the presence of anti-malware defences, implementation of multi-factor authentication for administrative access, adherence to patching processes, and inclusion of a suitable GDPR privacy notice.
Along with the initial documents, we also submitted information on our web dependencies, Software Inventory and Hardware Inventory. Our app, infrastructure, and documentation were assessed across critical security domains, including Application Security, Operational Security, and Data Handling Security and Privacy. Each domain has specific key controls, and our task was to ensure our practices aligned with these controls.
The hands-on guidance provided by Microsoft’s team extended beyond generic instructions. More than just providing instructions, Microsoft’s team took on the role of guides, offering insights and advice that extended beyond the immediate requirements of compliance. Microsoft’s commitment to friendly guidance was a defining factor in our certification experience.
A distinctive advantage of our Microsoft 365 app compliance journey is the leadership role assumed by Microsoft, ensuring an independent and impartial auditing process. This external and independent perspective, coupled with Microsoft’s industry expertise, contributes to the objectivity of the process, assuring stakeholders and users that the certification decisions are driven solely by adherence to stringent criteria rather than internal considerations. Complementing our security measures was Microsoft’s complimentary third-party penetration testing, conducted by external experts. This rigorous testing involved simulated attacks to identify potential vulnerabilities, underscoring Microsoft’s commitment to providing startups with robust security measures without financial barriers.
The impact of Microsoft 365’s compliance program extends beyond internal operations; it serves as a pledge to our customers, emphasizing our unwavering commitment to safeguarding their data with utmost care and aligning with industry best practices. This certification is not merely a badge; it is a statement resonating with our customers, fostering trust and confidence in our ability to safeguard their data.
Looking Forward
Rather than viewing this certification as the end of the road, it serves as a springboard to propel us toward even greater heights. The experience and knowledge gained from the Microsoft 365 App Compliance Certification have set the stage for our future pursuits. We’ve recognized that this certification not only fortified our data security and privacy measures but also equipped us with the know-how to navigate the complex world of compliance standards.
As we look to 2024, our sights are firmly set on attaining industry-standard security certifications, with SOC2 Type 2 being a prominent goal on our security roadmap. The foundation laid during our journey with Microsoft 365 App Certification has made this much more achievable.
Armed with the insights, practices, and rigorous processes we’ve adopted, we’re confident that we can approach future certifications with a more streamlined and informed approach. The lessons learned from our initial security certification will serve as a valuable template, ensuring that our commitment to data protection remains unwavering and our path to certification excellence remains well-defined.
Conclusion
While compliance is undoubtedly a crucial aspect of any good security framework, it alone does not guarantee foolproof protection. The implementation of these security frameworks with the right security controls and independent assessments plays a pivotal role in this process.
Going beyond the checkbox mentality of compliance, these assessments provide a comprehensive and objective evaluation of an organization’s security posture. By engaging with a reputable entity like Microsoft for independent evaluations, startups can gain insights into their strengths and weaknesses from an unbiased perspective.
By taking the necessary steps, including the Microsoft Publisher Attestation and the comprehensive compliance certification, software startups can build trust, secure sensitive data, and establish themselves as reliable partners for enterprises and we recommend other startups to do the same!
Did you know that a staggering 75% of security breaches involve a human risk factor? (Verizon DBIR Report 2023) This statistic underscores the critical importance of addressing insider threats within your organization.
Join us for this enlightening webinar to uncover valuable insights on insider risk mitigation and embrace the necessary shift in mindset to foster a culture of strong IT security.
During this webinar, we will delve into the key insights provided by industry expert Ganesh Krishnan, the CEO and founder of Anzenna. With a remarkable track record of successfully implementing security policies during his tenure as a CISO and Head of IT Security at organizations like Atlassian, LinkedIn, and Yahoo, Ganesh is well-equipped to guide us.
One of the central themes of the webinar is the significance of adopting a human-first approach in the ongoing battle against online threats. This approach acknowledges that employees, whether intentionally or unintentionally, can pose significant risks to your organization’s cybersecurity.
By comprehending the human element of security, you can develop strategies to better safeguard your data and assets from both negligent employees and those with malicious intent.
The webinar will equip you with practical frameworks aimed at effectively mitigating insider risks. These frameworks are designed to reshape your perspective, moving from a reactive stance to a proactive approach to managing insider risk within your organization.
In conclusion, it cannot be stressed enough how vital it is to address insider risks. With the continually advancing sophistication of cyber threats, adopting a human-centric approach to security is not just an option – it’s a necessity.